Welcome to all the new subscribers over the last few weeks! You can read my last article on Ethereum’s layer 2 scaling solutions here.
Stay up to date with Superfluid by subscribing here:
This edition of Superfluid is brought to you by DAO Under ….
Despite claiming to be fully distributed, web3 is predominantly run in North American and European timezones. Those in the Asia-Pacific (APAC) region face major geographic and timezone hurdles to participate within the web3 ecosystem. Working at 3 am is simply unsustainable.
We want to change this.
We’re building your web3 home in APAC. DAO Under is a safe, inclusive space for all creators, participants, or keen learners to leave their mark on web3. We will help foster real connections both virtually and in person. We aspire to be the best support group you could ever wish for.
You can keep up with DAO Under on Twitter
Now on to this week’s article :)
For anyone new to the space, dealing with crypto transactions can be confusing. Needing to install MetaMask and dealing with weird addresses filled with numbers and letters are pretty annoying, but the worst part is the siloed nature of individual blockchains.
Each blockchain is like a railroad. It goes straight and doesn’t deviate from its intended path. However, in a world that craves interoperability and flexibility, this doesn’t compute. Transacting within a specific ecosystem all work to a decent standard, interactions between these blockchains can be tough and intimidating for new entrants.
If only there were Bridges between each chain.....
What is a bridge?
Like the real world, bridges in crypto facilitate the sharing of data and traffic between two chains. This helps make siloed blockchains interoperable. It doesn’t make sense to restrict access to certain dApps because a user doesn’t own that ecosystem’s main token. As such, bridges are key to increasing the rate of adoption.
Individual ecosystems are powerful and have their own unique characteristics. Developers factor this in when deciding on which blockchain they should build their dApp on. However, this inherently makes it difficult for users across different ecosystems to use their dApp, which in turn can reduce the dApp’s user pool. As such, this might push developers to use blockchains that have more volume and attention but are less suited to building their dApp, which can constrain product development.
Bridges are important because they give users the flexibility to interact with dApps in the way they want. They allow users to get more out of the assets they own without having to sell existing assets or convert fiat into crypto. They can also unlock new use cases and opportunities for users to take advantage of.
So how do they actually work?
There are three different ways bridges work:
The Mint and Burn: A very basic implementation of a bridge from Chain A to B is structured like a vault or escrow style implementation. The bridge receives tokens from Chain A and locks them in a smart contract. It then mints an equivalent amount of fresh tokens (aka ‘wrapped’ tokens like wETH or renBTC) on Chain B. To recover your tokens, simply burn them on Chain B and unlock them on Chain A. In this scenario, the total amount of tokens never changes, however it is split across both chains.
Liquidity Pools: With the rise of DeFi, some bridges are borrowing the concept of liquidity pools to facilitate cross-chain asset transfers. Users would deposit tokens to a pool on Chain A and then withdraw tokens from a pool on Chain B. One key advantage here is that the assets provided by liquidity pools are native to Chain B rather than wrapped or synthetic assets which may not track the underlying asset properly. However, these bridges are only functional if there is enough liquidity staked in the pool.
Light Clients & Relays: In the previous two implementations, there is a need to have an intermediary blockchain to facilitate transfers and to validate the legitimacy of requests. With this implementation, this isn’t required instead using relayers that sends cryptographic proofs of transactions on Chain A to Chain B. With this proof, Chain B can parse the proof and determine whether the transaction was legitimately included on Chain A and then mint an equivalent amount of the asset on Chain B.
E.g. Let’s say we want to move from BTC to ETH. A user would send 1 BTC to an escrow address on the BTC chain and this is then mined in block 500,000. A relayer then compiles this proof and sends it to an ETH smart contract. This smart contract is running a light node that stores enough information to validate the authenticity of a transaction. Once the smart contract receives the proof, the smart contract checks it against its local view to determine whether the proof is valid.
Compared to the other two implementations this one is a lot more expensive as it needs to store a ton of data on Chain B.
Bridge architecture
Thinking about bridges from first principles, there are a few key characteristics they need to exhibit, with the most important being a highly secure network.
It’s possible to view bridge security on a sliding scale from Trusted to Trustless.
Trusted means that users are 100% reliant on the bridge operator to carry out their operations as advertised. Users are unable to recover funds in the case of an exploit or malicious activity in the network.
Bonded networks mean that users have some economic incentive to be good actors (i.e. they have posted collateral). However, users are unable to recover funds if malicious activity occurs because the collateral is subsequently burnt. The form of collateral is different between bridges, with different impacts on the security of the bridge as a result of the collateral chosen.
Insured networks also require collateral to be posted, however as the name implies, users are insured against bad behaviour as they receive the posted collateral in the event of misbehaviour.
There are also a few other characteristics that are important to consider when building a bridge.
Capital Efficiency: The amount of capital tied up when bridging to different chains. The Mint and Burn implementation is poor as it relies on a large number of tokens being locked up.
Speed: Time taken to complete a transaction. Given the simplicity of liquidity pools, this is the quickest bridge to use.
Connectivity: The number of chains that can be connected through the bridge. Mint and burn bridges are able to achieve breadth and scale here.
Statefulness: The ability to transfer different assets, and execute cross-chain contract calls. Obviously, the relay method is reliant on being very stateful.
Design tradeoffs
Whilst these bridges have brought us closer to interoperability, we are still far away from seamless cross-chain interaction. First and foremost, ensuring a secure network is key. Earlier this month, the Wormhole bridge was exploited for 120k wETH on Solana. Wormhole uses the mint and burn mechanism to bridge assets from different chains onto Solana. As a result, there was heavy trust in the operator to ensure the bridge was robust. Seeing such a large scale attack places a heavy cloud over the entire bridge ecosystem for lacking the necessary security to be trusted.
Whilst no one would say using a bridge in crypto is a super seamless experience, moving fungible assets cross-chain is straightforward. On the NFT side, however, it’s a bit trickier. Most NFT bridges at the moment use the mint and burn mechanism to all assets to move cross-chain. However, what's uncertain is how bridges preserve the transaction history of that NFT if it is bought and sold across different chains? One of the key benefits of NFTs is to be able to track their transaction history and ensure their legitimacy.
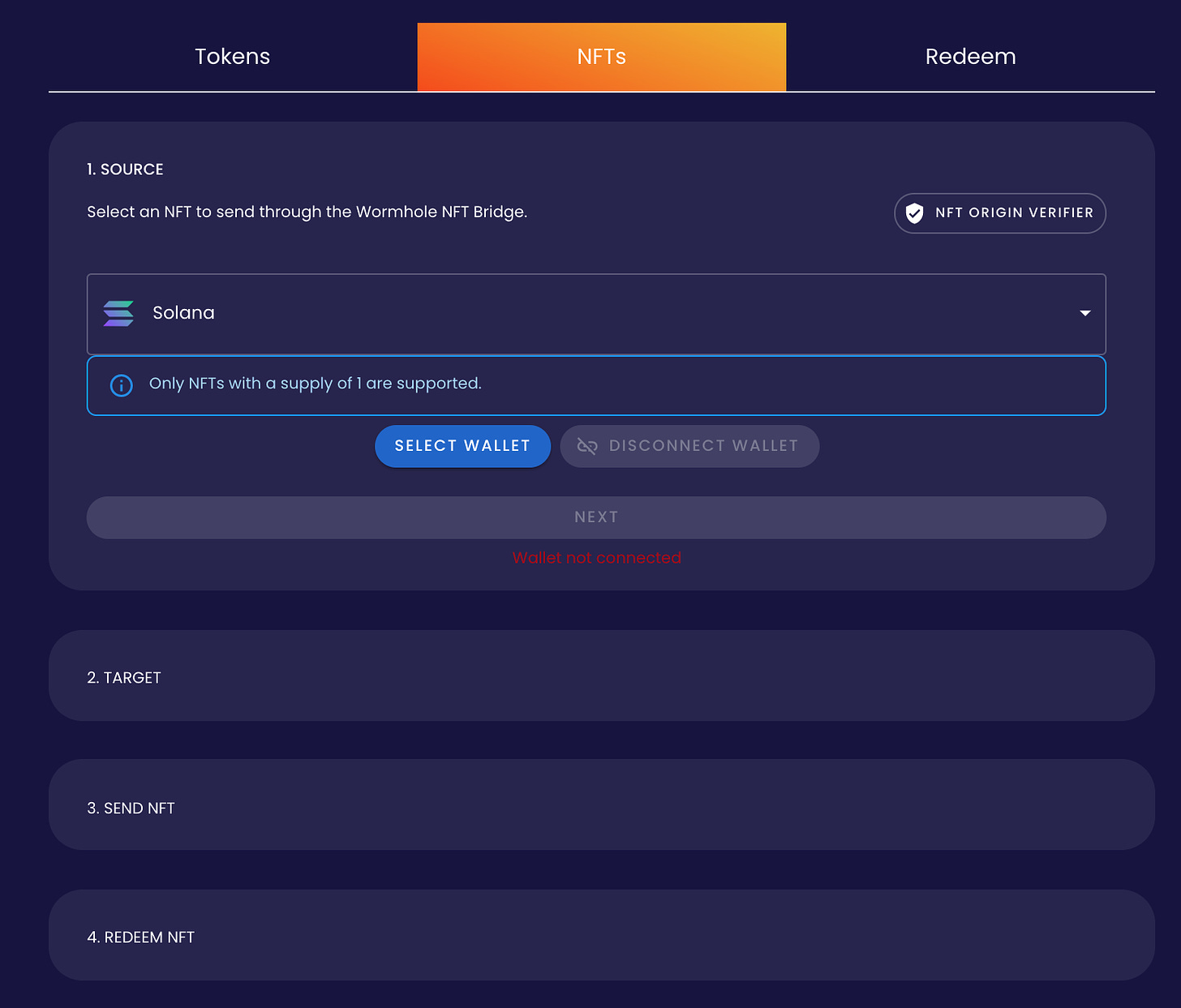
I tested Wormhole’s NFT bridge from ETH to Solana (potentially stupid to use a bridge that’s just been hacked 😬). As a crypto native, it was an OK experience, but it definitely could be improved with better communications. For instance, to get the NFT out of ETH, I had to approve two transactions totalling US$16 and to receive the NFT on SOL, I had to approve five transactions totalling US$0.95. Throughout this process, Wormhole had text indicating that I would need to approve multiple transactions but didn’t expand on why this was necessary. In a world where signing/approving random messages/transactions can drain your wallet, it’s better to have more – rather than less – language for users.
Now that my NFT is on the SOL network - I wanted to try and sell it, but alas it wasn’t recognised by either Solanart or Solsea 😟. Now, I’m not sure if there are any collections that have been deployed cross-chain, but it’ll be interesting to see whether this becomes standard practice as we move towards a cross-chain future.
Bridge ecosystem
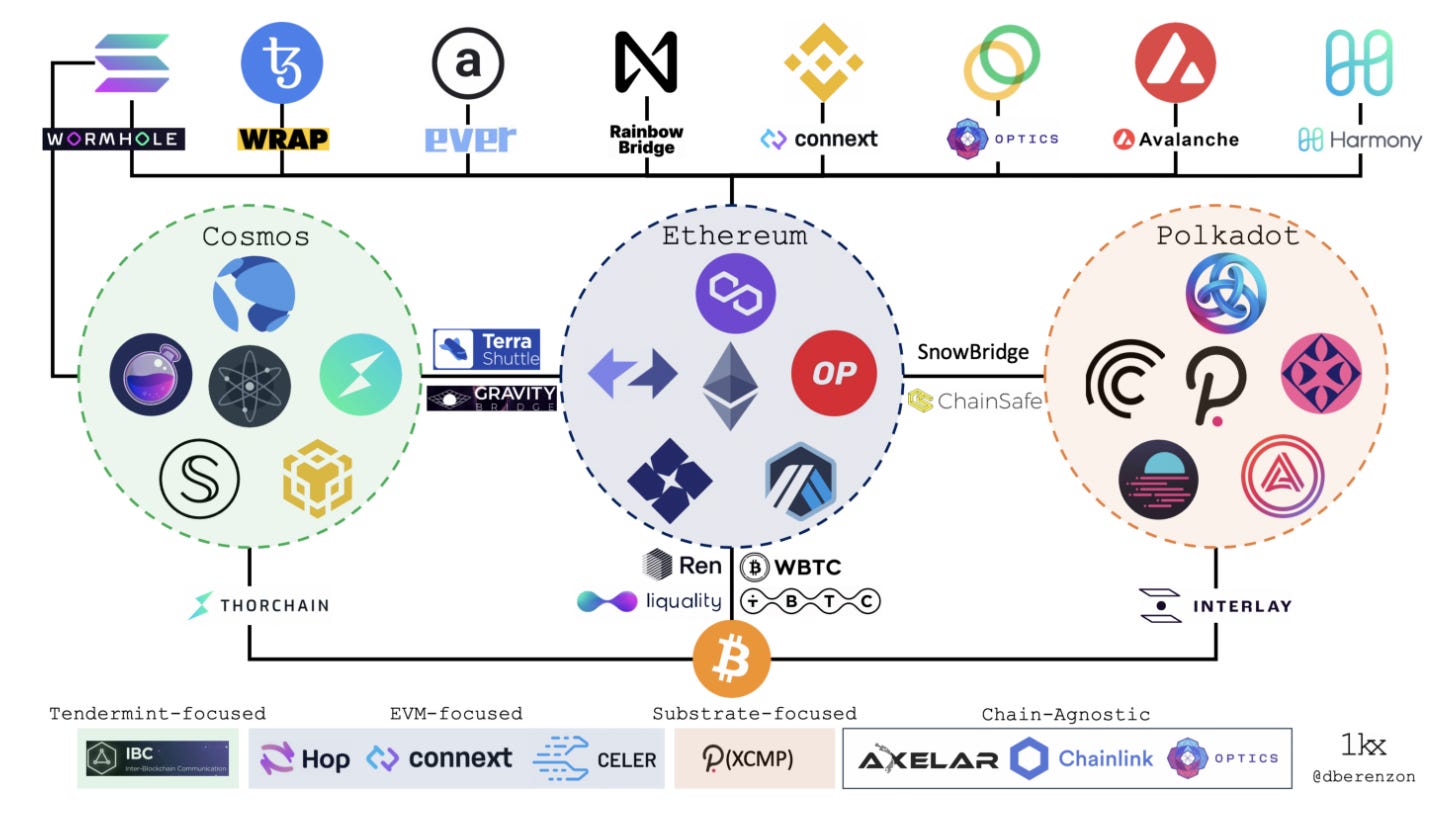
Similar to the proliferation of various Layer 1 blockchains, there are more than 60 different bridges out in the wild. They vary wildly from catering to more than 5 different chains to being specific to a single ecosystem.
App-Specific: A protocol that allows a dApp to plug and play a bridge without needing to handle hosting different blockchain instances
Chain Specific: A bridge between two chains that facilitates transfers and wrapping assets between chains.
Asset Specific: A bridge that deals with only one asset from a different chain. Usually uses a Mint and Burn mechanism to ‘wrap’ assets.
Cross-Chain: A bridge that traverses across many chains and can facilitate complex transfers across chains.
Are Bridges valuable?
From the market map above, it’s clear that the bridging ecosystem is crowded and competitive already for those facilitating cross-chain swaps. For this vertical, UX and flexibility (access to many chains) will be key to standing out from the crowd. Most of the bridges in this vertical collect revenue on a % of each transaction. As such, with so much competition, bridges are likely to either launch their own token that rewards holders or drop the rates of using the bridge. In either scenario, it’s likely that the bridge with the best security and greatest selection of chains will win. It’s a similar story for App-Specific bridges.
For the other verticals, there is a bit more defensibility embedded within the product. For Chain-Specific bridges, this affiliation will draw in users naturally due to it being embedded deep into a chain’s ecosystem. Likewise, for Asset-Specific bridges, given their close tie into a specific ecosystem and focus on one asset it will be harder for new entrants to break in.
Make sure to subscribe now to not miss the next article.
How did you like today’s article? Your feedback helps me make this amazing.
Thanks for reading and see you next time!
Abhi